Colorado justices narrowly uphold IP-based search warrant, decline to adopt broader rule
The Colorado Supreme Court upheld as constitutional on Monday a warrant that permitted Clear Creek County sheriff’s personnel to search a man’s laptop for child pornography, even though he lived in a unit separate from the target residence and law enforcement was focusing on a different suspect the day of the visit.
Previously, four lower court judges offered three different legal theories for why the warrant, based on the Internet Protocol address associated with the property, was constitutional. But the Supreme Court declined to adopt any of them. Instead, wrote Justice Melissa Hart, the simplest answer was that the warrant reasonably covered Kevin Matthew Dhyne’s basement apartment once Dhyne, himself, volunteered he used the IP address.
“In this case, the basis for probable cause was not particularly named individuals, but rather a particular IP address associated with a physical street address,” she wrote in the June 17 opinion. “Critically, Dhyne told the police that he used the IP address they were investigating, and he lived at that same physical address. His statements tied his apartment to the probable cause.”

Vivek Krishnamurthy, an associate law professor at the University of Colorado who cautioned the Supreme Court about IP-based warrants that sweep in too many devices or potential suspects, applauded the decision.
“I am delighted that with its ruling today, the Colorado Supreme Court has reaffirmed that reasonableness is at the heart of determining whether the issuance and execution of search warrants complies with the Fourth Amendment,” he said. “That said, I would have liked the Supreme Court to provide more guidance to help law enforcement agencies and the lower courts determine when different kinds of electronic searches are reasonable.”
Clear Creek County law enforcement obtained a warrant to search a home where child pornography was being downloaded through a specific IP address. Although they had pinpointed a particular suspect who lived at the residence, they unexpectedly encountered Dhyne, a tenant in the home’s basement, after showing up to execute the warrant. Dhyne revealed he, too, had access to the shared Internet network and police seized his computer.
They later found sexually exploitative material involving children on his computer and a jury convicted him.
The Fourth Amendment prohibits unreasonable searches and seizures, and requires warrants to describe with particularity “the place to be searched.” Dhyne originally sought to exclude the computer evidence from his trial, alleging the search and seizure were illegal because the warrant did not apply specifically to his home.
A trial judge agreed law enforcement violated Dhyne’s rights by continuing their search after learning about Dhyne’s separate residence. But the judge believed they would have inevitably gotten another warrant to search Dhyne’s computer because Dhyne admitted to using the same IP address where child pornography was being downloaded.
A three-judge panel for the Court of Appeals subsequently upheld that conclusion, but relied on its own rationales.
Judge Neeti V. Pawar, writing for herself and Judge Jaclyn Casey Brown, concluded the IP address was “used in common” across the property, so the search of Dhyne’s separate unit was authorized under the warrant.
Then-Judge David J. Richman, relying on federal cases, alternatively suggested that once Dhyne admitted to using the target IP address, the “entire premises were suspect,” including Dhyne’s unit.

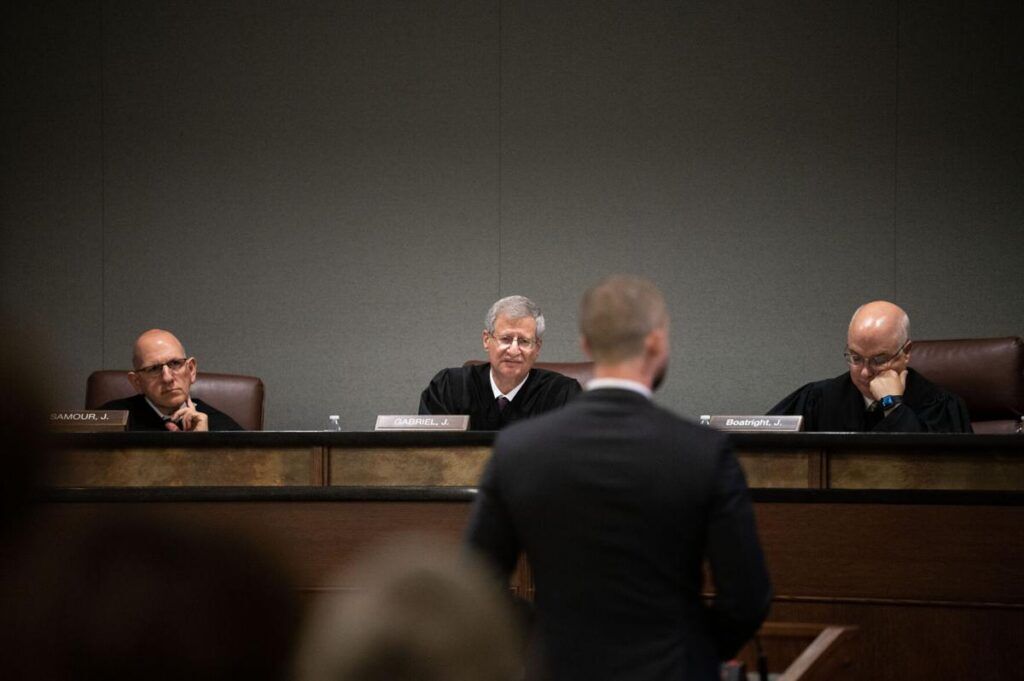
Colorado Court of Appeals Judges Stephanie Dunn, Neeti V. Pawar and Grant T. Sullivan listen to the case of People v. Dooley at Fort Lupton High School on Tuesday, April 2, 2024 in Fort Lupton, Colorado. The Colorado Court of Appeals and Supreme Court hold "Courts in the Community" events for students to learn about the justice system and hear real cases. (Rebecca Slezak For The Denver Gazette)
Rebecca Slezak

Colorado Court of Appeals Judges Stephanie Dunn, Neeti V. Pawar and Grant T. Sullivan listen to the case of People v. Dooley at Fort Lupton High School on Tuesday, April 2, 2024 in Fort Lupton, Colorado. The Colorado Court of Appeals and Supreme Court hold “Courts in the Community” events for students to learn about the justice system and hear real cases. (Rebecca Slezak For The Denver Gazette)
Turning to the Supreme Court, Dhyne urged the justices to reject all three justifications. He argued the wireless network at the property had an open connection, meaning anyone could log on without a password. With pedestrians and cars passing by, an “infinite amount of people” could be subject to a search.
Krishnamurthy, who submitted a legal brief with two other law and engineering professors, raised similar concerns about network-based searches, warning that the rise in mobile devices “reduces the likelihood that one that was used to engage in criminal activity using a particular internet connection will be found at the location associated with the connection.”
The Supreme Court ultimately decided that an IP address’s common use or its potential to render the entire premises suspect did not matter thanks to Dhyne’s own statements to police.
Although there were “facts pointing in both directions — for and against an additional warrant being required,” Hart wrote, law enforcement “reasonably decided that the warrant included the basement apartment. We will not invalidate a search under these circumstances.”
Declining to address IP-based searches more broadly, including the scenarios Dhyne raised on appeal, Hart added the Supreme Court should “avoid creating new rules that could be strained by future technological advances or factual scenarios.”
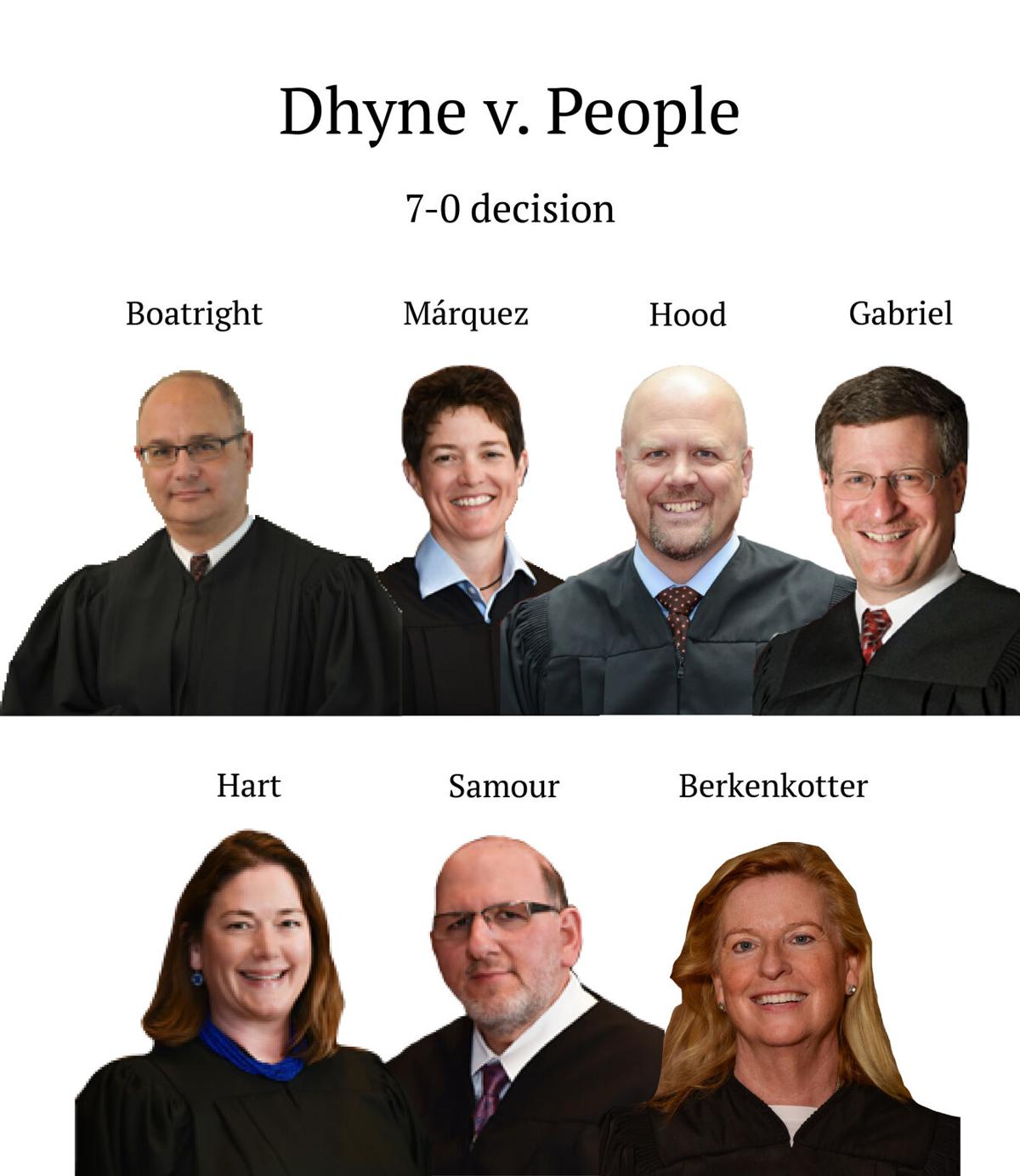
The case is Dhyne v. People.